Test your deployment with MFA enabled¶
Warning
You should have received an email or teams chat from your SA/SME to continue.
Close any opened browser and re-open
Microsoft EdgeConnect to
Bluesky. Don’t try withVanillaas your MFA test account does not exist in on-prem AAD. Thus, the SSo will not work. You can add this user in ADDS if you are confident with AD.If you are not prompted at Azure AD login page, open an
incognito window. It means you still have Azure AD cookies from previous session with ``user1``account.At prompt, login with your MFA account. In my case,
matt@f5access.onmicrosoft.comand the password provided by your SA/SMEYou will be asked to enroll and select an MFA method

Click
NextYou have the choice to use the
Microsoft Authenticatormobile app, or useSMS. Make your choice and follow the step to enroll your device (or phone number)
I select the
mobile app, scan theQR code, andapprovethe push notification on my mobile phone.I click
NextandDone
Azure AD asks you to
change your passwordset by your SA/SME.When done, and redirected to
Bluesky, you can notice it does not work. The user has to be assigned with theBlueskyapp.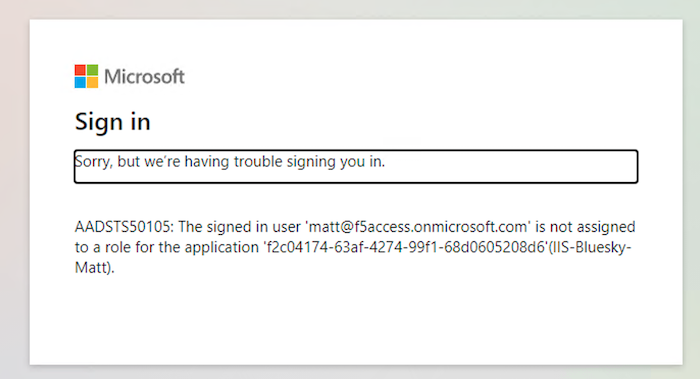
In the BIG-IP, edit the
ISS-Bluesky-<my name>template, and inAzure Active Directorystep, add your account.
Click
Save and NextandDeploy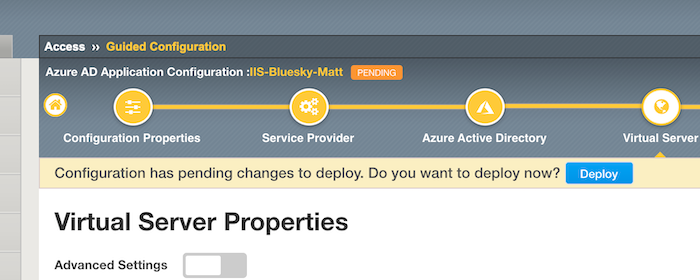
Make a new test, approve the
push notificationor enter theOTPreceived by SMS.
Note
This lab is not Azure AD Conditional Access. This is just user MFA. Conditional Access is similar but it is tied to a policy (group, location, app …). In this lab, matt will be prompted for MFA whatever the apps he connects to.